I almost laughed at first.
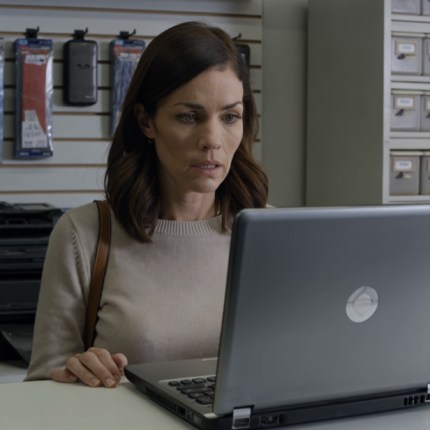
“Excuse me?” I said. “It’s just a broken laptop. My son uses it for work.”
The technician didn’t smile.
He kept his voice low. “Ma’am… I’m serious. You need to cancel your cards. Change your passwords. Now.”
Something in his face—tight, pale, genuinely shaken—made my stomach drop.
“What did you find?” I asked.
He hesitated, glancing back toward the counter where the laptop sat open.
“Things I shouldn’t have seen,” he said. “And things you definitely shouldn’t ignore.”
—
I felt a cold weight settle in my chest.
“That’s my son,” I said, quieter now. “You need to explain.”
He swallowed. “I started a routine check—hardware, storage, nothing unusual. But when I opened the system… there were hidden folders. Encrypted. Not uncommon, but…”
“But what?”
“They weren’t just protected. They were active.”
—
I didn’t understand. “Active how?”
He lowered his voice even more.
“Remote access tools. Keyloggers. Scripts that connect to other machines. And… lists.”
My hands went numb. “Lists of what?”
He met my eyes.
“Names. Emails. Password strings. Banking log formats.”
—
The room tilted.
“That doesn’t make sense,” I whispered. “He’s just—he’s a kid.”
“I’m not saying he built all of it,” the technician said carefully. “But this laptop has been used for things that can ruin people. Financial theft. Identity access. Maybe worse.”
I shook my head. “No. You’re wrong. You have to be.”
“I hope I am,” he said. “But I’ve seen enough to know you’re at risk if your information is anywhere near this device.”
—
My first instinct was denial.
The second… was fear.
Because suddenly, little things didn’t feel so little anymore.
The times he’d asked to “borrow” my card for online purchases.
The way he always insisted on setting up accounts for me.
How he knew when my passwords “needed updating.”
—
“What do I do?” I asked, my voice barely holding together.
“Right now?” the technician said. “Protect yourself.”
He started counting quietly on his fingers.
“Cancel your cards. Change every password—from a different device. Enable two-factor authentication. And don’t confront him until you know exactly what you’re dealing with.”
“Why not?” I asked.
He hesitated again.
“Because if he is involved in something like this,” he said, “he’ll know how to cover it up the second he suspects you’ve found out.”
—
My heart broke a little at that.
Not just from fear.
But from the possibility that the boy I raised… wasn’t who I thought he was anymore.
—
I looked over at the laptop.
It sat there, quiet. Ordinary. Like any other broken machine.
But now it felt like something else entirely.
Like a door I wasn’t ready to open.
—
“Can you fix it?” I asked weakly.
The technician shook his head.
“That’s not the problem here.”
—
I nodded slowly, picking up my bag.
“Thank you,” I said, though the words felt heavy.
As I turned to leave, he added one last thing:
“Ma’am… whatever you do next—do it carefully.”
—
I stepped outside, the world suddenly louder, harsher.
And for the first time since I became a mother…
I wasn’t worried about protecting my child.
I was worried about protecting myself from him.